[2013 Version] Starting a Pentesting Lab [How-To/Linux/Windows]

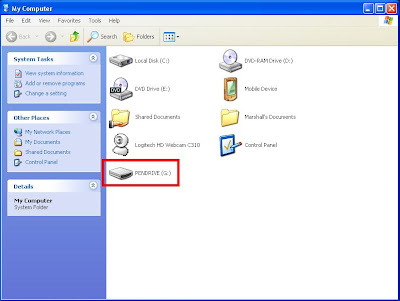
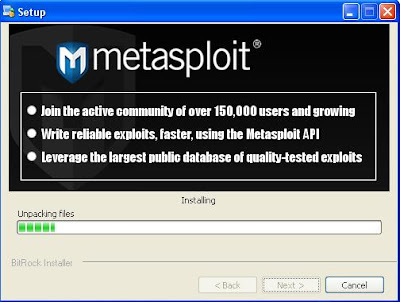
Recently I bought a gaming computer with some of the best specs out there (i7, gtx670, 16gig ram, ssd, etc) and decided to finally set up my own Pentesting lab so I can practice breaking and securing "real" boxes of my own. My current setup consists of my router connected to my apartment's WAN using DHCP, which issues private DHCP leases to the connected boxes on my network. I have a Windows 7 laptop of my own, a Windows 7 desktop host machine running VMs, and a Ubuntu 12.10 server for all my main Linux needs (I have SSH set up so I can access this box from work and other places). My friends also connect to this network via Wifi, so there are random Win7 and OSx computers connected to it. As for my virtualized boxes, I have Windows XP (different SPs), Windows Server 2003, 2008, and 2012, Metasploitable 2, DVL (Damn Vulnerable Linux), BackTrack5R3 (I hack from this box), and a few other exploitable machines. I will be setting up a Windows Vista and a couple other *nix...